Time to read: 4 minutes.
ISBN 978-0-9842789-1-6
Published April, 2011.
No longer available.
About This White Paper
This is the first comprehensive document that discusses end-to-end security recommendations and best practices for the Adobe Flash Platform in enterprises. The white paper was written independently, so the information is presented without vendor bias. Code fragments are used to illustrate specific issues, and links to documentation are provided to back up advice. Because computer security is a multidisciplinary topic, this white paper provides a roadmap to other resources.
This white paper is a valuable resource for all ActionScript-based projects, including Flex, BlazeDS and the entire LiveCycle family.
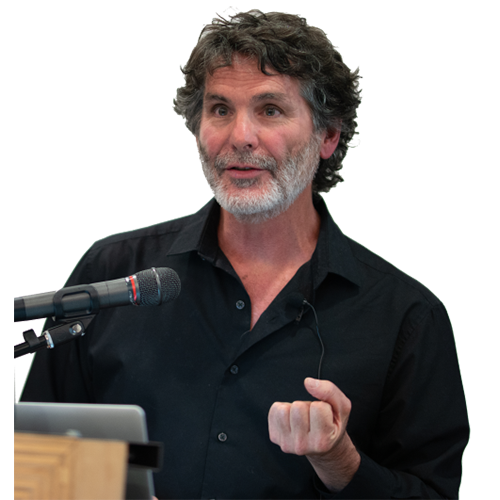
Much of the security documentation from Adobe is focused on the Flash Player client. There is a lack of comprehensive information about security for the entire Adobe Flash Platform. Michael Slinn, a well-known enterprise Flash Platform expert has produced a detailed roadmap, interviewed Adobe technical staff, reconciled the documentation sources and cross-referenced the information with well-known security experts.
With the introduction of Flash Player 10, Adobe greatly enhanced client-side application security for Flash applications. Flash is by nature a client-server technology, so end-to-end security for an application based on the Adobe Flash Platform must also include server-side considerations, and the connection to the server. This document discusses end-to-end client/server security for distributed computing systems built with the Adobe Flash Platform. Special consideration is given to enterprise issues security issues, and to cloud computing (Amazon Web Services.) Details of how to comply with the new NIST security standards, a new requirement for providing IT products and services to the US federal government, are provided.
Target Audience
This white paper is intended for enterprise IT operations, system integrators and software developers.
Acknowledgements
Thanks to:
- Peleus Uhley, Platform Security Strategist at Adobe Systems;
- Seth Hodgson, Software Engineer at Adobe Systems;
- Lori Mac Vittie, Senior Technical Marketing Manager at F5 Networks
- Jeremiah Grossman, CTO at WhiteHat Security and Jason Calvert, Security Engineer at WhiteHat Security.
Contents
- Cross-domain security – definitions, scenarios and code fragments.
- OWASP top ten security issues applied to the Adobe Flash Platform.
- Injection via FlashVars, JavaScript/ActionScript interaction and data validation.
- Cross-site scripting; Flash clients are vulnerable to reflected XSS attacks.
- Broken authentication and session management; session hijacking.
- Insecure direct object references; how to safely use
Security.allowDomain(), and to securely configure LiveCycle Data Services ES assemblers. - Cross-site request forgery; invisible to users when Flash Player is attacked.
- Security misconfiguration; best practices.
- Insecure cryptographic storage; NIST recommendations.
- Failure to restrict URL access; SWF considerations.
- Insufficient transport layer protection; ciphers, AMF and RTMP considerations.
- Non-validated redirects and forwards; phishing attacks with SWFs.
- SSL/TLS ciphers and NIST.
- ActionScript and Flex.
- BlazeDS and LiveCycle Data Services ES (LCDS) security configuration.
- Channel configuration for HTTP
- Security aspects of the 5.5 members of the RTMP family of protocols.
- Java servlet container considerations, including Tomcat 6 and 7.
- Cloud Computing security issues.
- List of security testing tools for the Adobe Flash Platform.
- References for all the topics discussed.
Accolades


From Heidi Williams, Group Product Manager, Flex Enterprise Customers and Partners at Adobe Systems:
Mike Slinn is a trusted source that we know does his homework thoroughly.

From Lori Mac Vittie, Senior Technical Marketing Manager at F5 Networks:
While there are many resources discussing end-to-end security in a generic architectures there are none that delve into the specific challenges associated with Adobe Flash Platform despite its broad use across a variety of vertical industries.
This white paper fills an unmet need for system integrators and enterprise IT departments for up-to-date, concise advice on building and deploying secure applications built with ActionScript. It is also highly relevant for applications built on related Adobe products such as Flex and AIR Rich Internet Applications (RIAs).
This publication will be of particular interest to those who directly or indirectly conduct business with the US Federal Government.
Did you know?
As of Jan 1, 2011 NIST sets the security standards for the US federal government. All software sold to the US federal government must comply. NIST requires stronger SSL/TLS ciphers than are commonly used today.
This white paper describes how to configure the Adobe Flash Platform to use NIST-compatible ciphers for SSL/TLS.
Cross-domain policies that reference certain pages might introduce a new security risk.
Software professionals who work with the Adobe Flash Platform generally assume that a properly designed
crossdomain.xml does not introduce any additional security concerns.
Learn why a common programming practice opens up a new security weakness when a crossdomain.xml
file is present.
Adobe AIR applications are more secure than Flash Player web applications.
The interaction between a web browser and its plugins presents security risks. Half of the OWASP Top Ten Security Risks for 2010 are affected. The white paper details steps to take for each of these security risks.
Cloud Computing can be made secure.
Default settings are not secure. This white paper discusses how to make them secure, without adversely affecting performance.
Rogue Flash / Flex web applications can inject JavaScript into their host web page.